GDPR requirements your engineers and AI agents can actually implement.
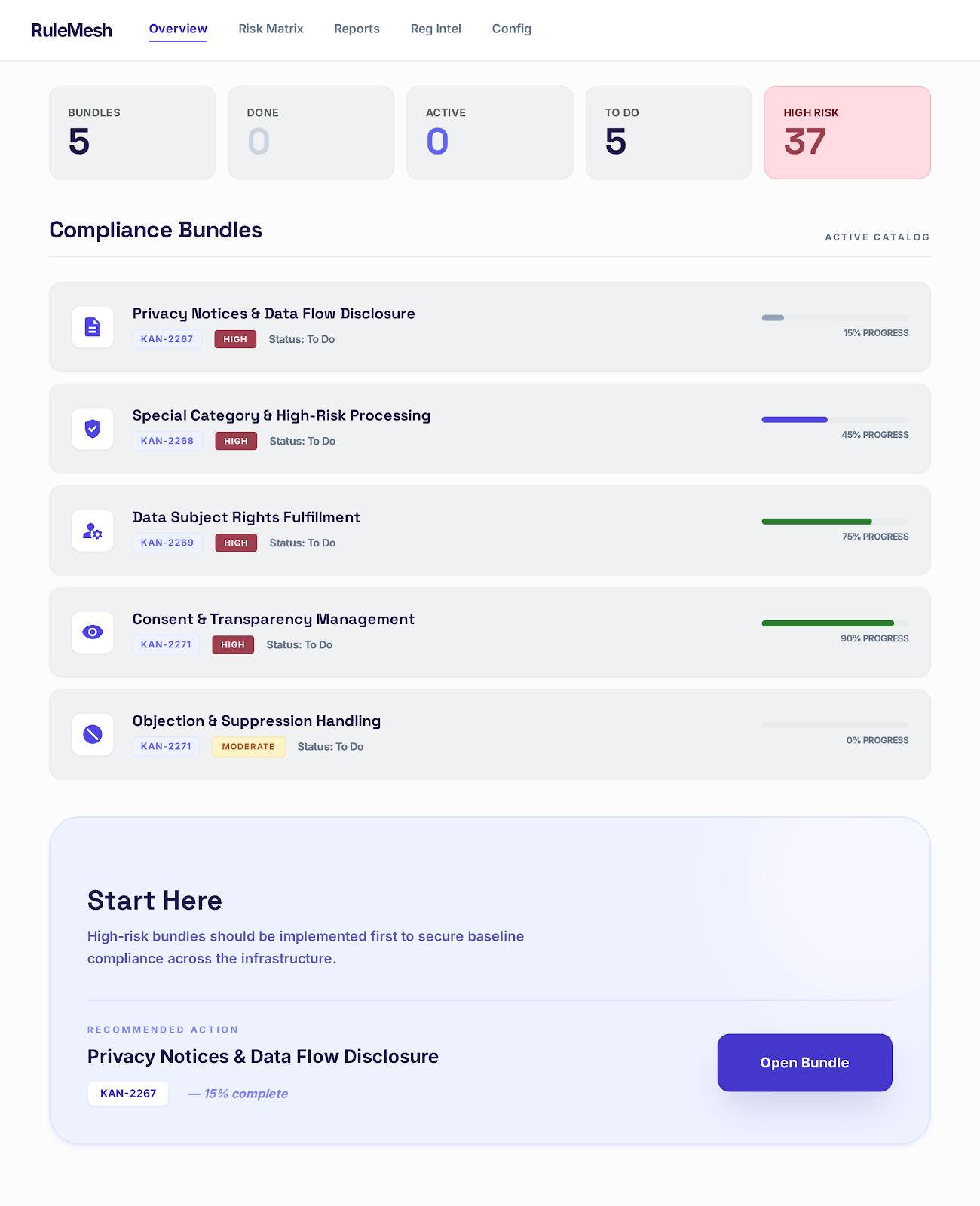
RuleMesh defines what to implement across your cloud infrastructure, how to execute it with framework-specific controls, and what evidence proves it was done — ready for engineers and AI agents.
credit_card_offLocal scan. No source uploaded. No credit card required to get started.
GDPR posture · landingpage
Partial security measures detected: HTTPS transport, JWT authentication, password policy enforcement, account lockout handling. Missing: formal risk assessment, documented security measures catalog, regular review process.
The missing layer between the policy and the system.
Legal teams read the law. Engineering teams build the system. Auditors verify after the fact. The technical specification that should connect those three usually does not exist.
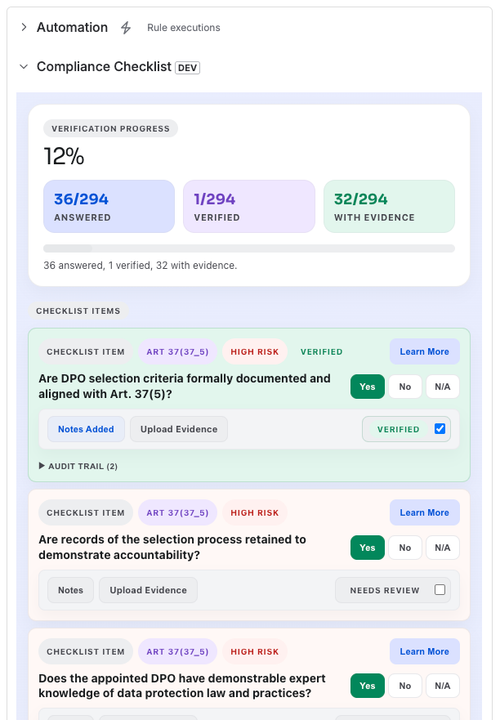
RuleMesh defines the requirement from source law, maps it to the control pattern the team should implement, and specifies the evidence a reviewer will expect before the audit starts.
What the law requires
A structured requirement with citation back to the GDPR article and paragraph. When someone asks where it came from, the answer is the source text.
What engineering should do
The control pattern that satisfies the obligation, mapped to the cloud and security frameworks your team already uses.
What evidence proves it
The artefact, log, configuration, or attestation a reviewer will expect to see. The evidence is specified before the work starts, not reconstructed later.
From one MCP command to a shareable evidence signals report.
Four steps. Minutes apart. Local scan. No source uploaded.
Connect your agent
One command adds RuleMesh to Claude Code, Cursor, or any MCP-compatible agent.
→Scan your codebase
Your agent evaluates the repo against 192 GDPR IT requirements and records evidence signals locally.
→Generate the evidence signals report
The output shows what was found, what is partial, and what is missing across the relevant GDPR bundles.
→Track the work in Jira
Findings become Jira tickets with verification checklists and evidence tracking.
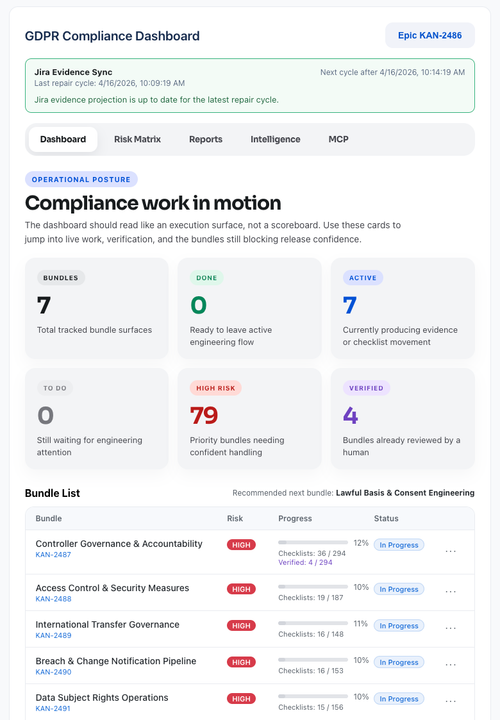
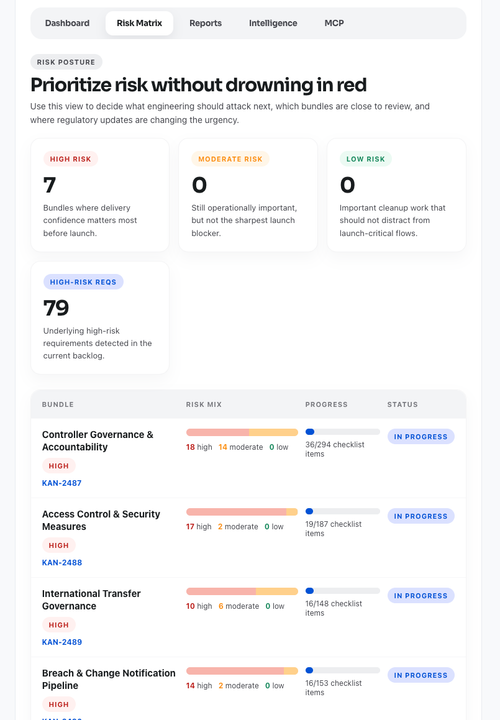
Turn evidence signals into verified engineering work.
What happens in Jiralive
The agent scans locally and reports evidence signals into Jira tickets. Bundle coverage becomes visible, checklists update, and the team works from the same requirement set.
Why Jirafirst integration
Engineers do not want another dashboard. The work should land in the system where engineering already plans, ships, and reviews.
Privacy by designread-only · local
RuleMesh never accesses source code. Scans run locally via your AI agent. Only file names and signal scores are reported.
192 GDPR requirements. 7 engineering modules.
We decomposed 99 GDPR articles into structured requirements mapped to cloud controls, security frameworks, and evidence checklists.
Start from the regulation surface when the question is scope, terms, or next actions.
These pages are for teams working out applicability, definitions, and obligation scope before implementation begins.
GDPR Checker
Find out whether GDPR likely applies, which role you play, and what the engineering work looks like next.
Open surfacearrow_forwardGDPR Hub
Use the engineering-facing read of GDPR to understand scope, key terms, and the obligation clusters that matter first.
Open surfacearrow_forwardAI Act Hub
Get the terms, roles, and value-chain obligations that shape how AI systems are built, shipped, and governed.
Open surfacearrow_forwardWe are not building another compliance portal.
RuleMesh turns cited obligations into structured rules systems can act on. We are also authoring HCAP, an open protocol for machine-verifiable compliance between systems. The point is larger than document management: compliance should move out of paper policies and into the infrastructure itself.
Inside the company
RuleMesh helps teams implement requirements, map them to controls, and produce evidence signals in the workflow they already use.
Between companies
HCAP is the protocol layer for proving compliance posture across API and organizational boundaries without relying on email chains, questionnaires, and static agreements.
Open by design
HCAP is an IETF draft because compliance infrastructure should be interoperable. We would rather help define the category than trap verification inside a vendor-owned service.
Agent-Agnostic Compliance: how three AI models interpret identical regulatory data via MCP.
Our technical study explores the elimination of “agent drift” in regulatory mapping. Using structured MCP servers, we achieved consistent compliance coverage across Claude, Gemini, and GPT.
Read the White Paper→A fit if you are implementing now.
RuleMesh is onboarding a small number of teams using GDPR in real engineering work this quarter. If that is your situation, the next page should help you decide quickly.
Real implementation window
Your team has engineering capacity to act in the next quarter, not just research the problem.
Real GDPR surface
You process EU personal data and need an implementation path you can defend, not another policy exercise.
Workflow-first adoption
You want to start with the MCP path now, and use Jira if it fits your workflow today while other surfaces expand.
Not a fit if you only want attestations, outsourced compliance services, or a broad multi-framework rollout before GDPR is working in practice.
See if your team is a fit→Run the local scan first. Apply if your team is a fit.
Start with a free local scan on your own codebase. If your team is actively implementing GDPR and wants a closer working relationship, the design partner path is on the next page.